15 Free Best OSINT Tools for People and Face Search | Top OSINT Tools
OSINT tools have quietly become one of the most powerful assets for anyone working with digital information, whether you are verifying identities, investigating online profiles, or simply trying to stay safe in an increasingly connected world.
Over the years, I’ve seen how quickly the internet has evolved from a place of casual interaction into a dense network of data trails, where every profile, image, and interaction leaves behind clues. That’s exactly where the best OSINT Tools come into play—they help you cut through the noise, validate what’s real, and uncover insights that are often hidden in plain sight.
In this article, you will learn how the best OSINT Tools simplify complex investigations, which free tools actually provide reliable and actionable data, and how these tools are shaping everything from cybersecurity practices to modern app development and online platforms.
The demand for OSINT capabilities is growing at a rapid pace, and it’s not just limited to security professionals. According to Statista, global cybersecurity spending is projected to exceed $300 billion by 2027, reflecting how critical data intelligence and verification have become in today’s digital ecosystem. This growth also directly impacts areas like dating platforms, creator economies, and even the development cost of modern applications.
With that context in mind, let’s take a closer look at what OSINT tools really are and why they matter more than ever.
- About OSINT Tools
- What’s The Need To Look for OSINT Tools?
- How OSINT Tools Transform People and Face Search
- Key Features of the Best OSINT Tools
- 1. OSINT Framework
- 2. Google Dorks
- 3. theHarvester
- 4. SecurityTrails API
- 5. BGPView
- 6. Recorded Future’s Vulnerability Database
- 7. Triage Malware Sandbox
- 8. Mitaka
- 9. Recorded Future’s Browser Extension
- 10. Have I Been Pwned?
- 11. BuiltWith
- 12. Shodan
- 13. SpiderFoot
- 14. Maltego
- 15. Nmap
- How OSINT Tools Impact App Development and Digital Platforms
- Best Practices for Using OSINT Tools Safely and Ethically
- Wrap up
- FAQs
About OSINT Tools
Open Source Intelligence, commonly known as OSINT, refers to the process of collecting and analyzing publicly available data to generate meaningful insights. While the concept may sound technical, the reality is quite practical. Every time you search for someone online, verify a profile, or trace the origin of an image, you are engaging with OSINT at a basic level.
From my experience, what makes OSINT powerful is not just access to data, but the ability to connect scattered pieces of information into a clear picture. The internet is full of publicly available data—social media profiles, websites, forums, leaked databases, and more. However, without the right tools, this data is overwhelming and difficult to use. This is exactly where the best OSINT Tools step in. They simplify complex data collection and turn raw information into actionable intelligence.
Over time, OSINT has evolved from a niche practice used by intelligence agencies into a widely adopted approach across industries. Cybersecurity professionals use it to detect threats and prevent attacks. Recruiters rely on it to verify candidates. Journalists use it for investigations, and businesses apply it to monitor competitors and market trends. Even individuals now use OSINT tools for personal safety, especially when interacting on platforms like dating apps or exploring unfamiliar online profiles.
Modern OSINT tools are designed to automate and accelerate this process. They can scan thousands of data points within seconds, identify connections between people, and even perform reverse image searches using advanced algorithms. Tools like PimEYE, Social Catfish, and Yadex have made face and image search more accessible, allowing users to track where an image appears across the web.
Another important shift I’ve noticed is how OSINT is now closely linked with technology development. Whether it’s building secure platforms, reducing fraud in hookup apps, or optimizing identity verification systems, OSINT plays a key role behind the scenes. It also influences app development strategies, especially when developers want to integrate data intelligence features without significantly increasing costs.
In simple terms, OSINT tools help you make smarter decisions using data that is already out there. You just need the right approach and the right tools to unlock its full potential.
What’s The Need To Look for OSINT Tools?
If you’ve spent enough time online, you already know how easy it is for anyone to create a digital identity. Profiles can be built in minutes, images can be reused, and information can be manipulated. This is exactly why OSINT tools are no longer optional—they’ve become a necessity.
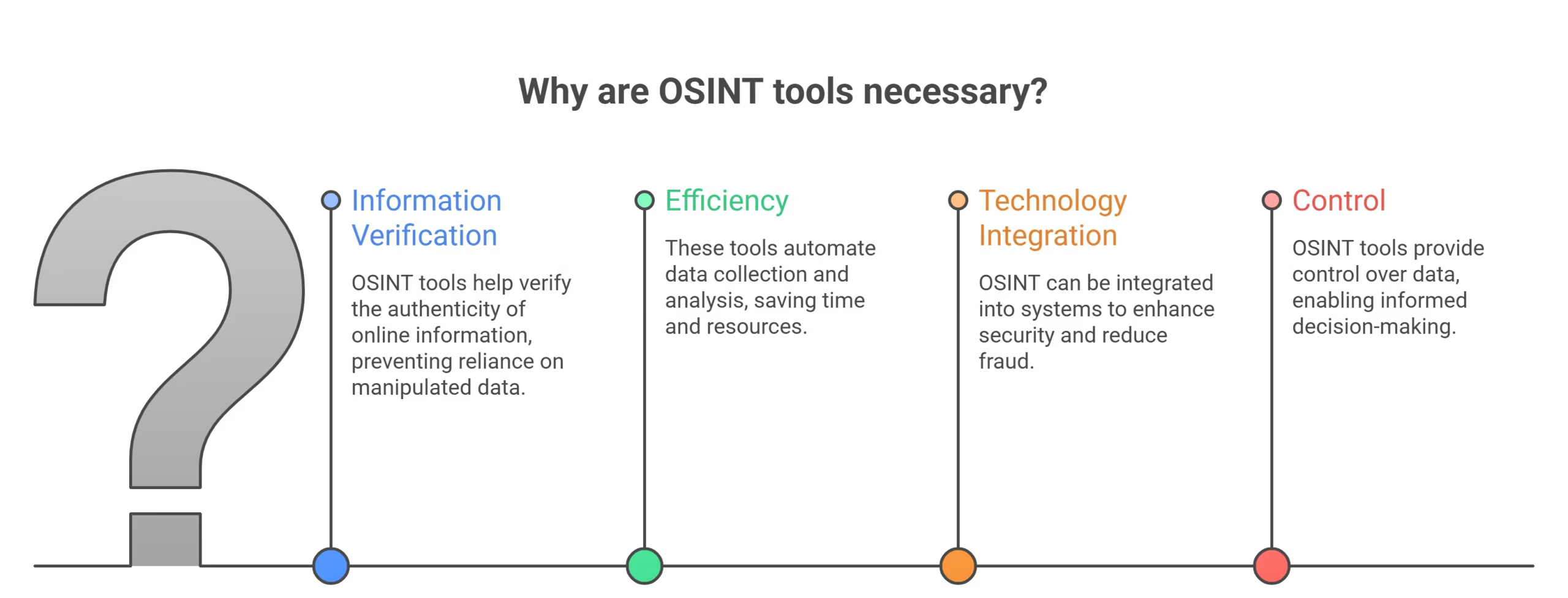
From practical experience, one of the biggest challenges today is not finding information, but verifying whether that information is real. Whether you are checking a suspicious profile, validating someone from a dating app, or researching a potential business contact, relying on surface-level data is risky. The best OSINT Tools help you go deeper. They allow you to cross-check identities, trace digital footprints, and uncover patterns that are not immediately visible.
The need becomes even more critical when you look at how online interactions have shifted. Platforms like social media, creator ecosystems, and even hookup apps are filled with users from around the world. While this creates opportunities, it also opens the door to fake profiles, scams, and identity theft. Tools such as Social Catfish are widely used today to perform reverse image searches and verify whether a person’s photos are genuine or reused elsewhere.
Another key reason people turn to OSINT tools is efficiency. Instead of manually searching across dozens of platforms, these tools automate the process. They scan multiple data sources, collect relevant information, and present it in a structured way. This is especially useful for professionals who need quick and reliable insights, such as investigators, recruiters, and cybersecurity analysts.
There is also a growing connection between OSINT and modern technology solutions. Businesses are integrating OSINT capabilities into their systems to improve trust and security. For example, in app development, OSINT can be used to build smarter verification features. It can also help reduce fraud-related risks, which directly impacts things like dating app costs by minimizing the need for manual moderation and support.
Ultimately, the need for OSINT tools comes down to one simple factor—control. In a world where data is everywhere, these tools give you the ability to verify, analyze, and make informed decisions with confidence.
How OSINT Tools Transform People and Face Search
People search and face lookup have changed dramatically over the last few years. What once required manual effort and guesswork is now powered by intelligent systems that can scan, compare, and verify data within seconds. This shift is largely driven by the rise of the best OSINT Tools, which have made advanced search techniques accessible to everyone.
At the core of this transformation is reverse image search technology. Instead of relying only on names or usernames, you can now upload a photo and trace where it appears across the internet. This is where Top Image Search Engines play a crucial role.
This capability has become especially important in environments where identity matters the most. For example, on dating platforms, users often interact with strangers. Without proper verification, it’s easy to fall victim to scams or misleading profiles. OSINT tools help reduce this risk by allowing users to verify images and cross-check online presence before engaging further.
Another area where OSINT tools are making a strong impact is in content-driven platforms and creator ecosystems. With the rise of subscription-based platforms, verifying the authenticity of creators has become critical. Users want to know they are interacting with real individuals, and platforms want to maintain trust. OSINT tools support this by enabling quick identity checks and background validation.
Beyond individuals, businesses are also benefiting from these advancements. Many companies now integrate OSINT capabilities directly into their systems. Whether it’s for fraud detection, customer verification, or improving onboarding processes, these tools are becoming a core part of digital infrastructure. This is particularly relevant in app development, where adding built-in verification features can significantly enhance user trust without increasing operational complexity.
In simple terms, OSINT tools have turned people and face search into a precise, fast, and reliable process. Instead of relying on assumptions, you can now make decisions based on verified data, which is a major advantage in today’s digital world.
Key Features of the Best OSINT Tools
When you start exploring OSINT tools in depth, you quickly realize that not all of them deliver the same level of value. Some tools are fast but lack accuracy, while others provide deep insights but require technical expertise. From experience, choosing the right tool comes down to understanding the features that actually matter in real-world use.

1. Data Accuracy and Reliability
The foundation of any OSINT tool is the quality of its data. Since these tools rely on publicly available sources, accuracy becomes critical. A reliable tool does more than just gather information—it filters irrelevant data and presents only what truly matters. This is especially useful when you are verifying identities or conducting people searches, where even small errors can lead to wrong conclusions.
2. Speed and Real-Time Results
In many scenarios, time is a deciding factor. Whether you are investigating a profile or analyzing online activity, you need results quickly. Modern OSINT tools are designed to scan multiple sources simultaneously and deliver insights within seconds. This real-time capability makes them highly effective for both individuals and professionals.
3. Ease of Use and Accessibility
A powerful tool is only useful if you can actually use it efficiently. Some OSINT tools are complex and require technical knowledge, while others are built with simplicity in mind. The best tools offer a clean interface, guided workflows, and easy navigation. This allows beginners to get started quickly while still offering depth for advanced users.
4. Integration and API Support
As digital systems become more interconnected, integration has become a key feature. Many OSINT tools now offer APIs that allow them to connect with other platforms. This is particularly valuable in modern app development, where developers can integrate OSINT capabilities directly into their applications for better data analysis and user verification.
5. Scalability and Performance
Your needs may grow over time, and your tools should be able to keep up. Scalable OSINT tools can handle larger datasets and more complex queries without compromising performance. This is essential for businesses, researchers, and analysts who rely on continuous data monitoring.
6. Automation and Smart Intelligence
Automation is what truly elevates an OSINT tool. Instead of running manual searches repeatedly, advanced tools allow you to automate workflows. You can set alerts, monitor changes, and receive updates whenever new data appears. This not only saves time but also ensures that you stay informed without constant effort.
7. Security and Privacy Considerations
While using OSINT tools, it is equally important to ensure that your own data remains secure. Good tools follow proper security practices and respect privacy boundaries. They allow you to conduct research responsibly without exposing sensitive information.
In the end, the best OSINT Tools combine all these features into a seamless experience. They help you move from raw data to meaningful insights quickly and efficiently, which is exactly what makes them so valuable in today’s digital world.
1. OSINT Framework
The OSINT Framework is often the first tool experienced researchers turn to when starting an investigation, and for good reason. Instead of being a single tool, it acts as a structured directory that connects you to hundreds of OSINT resources across different categories. From usernames and email searches to social media analysis and deep web exploration, it provides a clear path to finding the right tool for any task.
What makes it particularly effective is its simplicity. You don’t need advanced technical skills to use it. The framework is organized in a tree-like structure, where each category expands into more specific tools. This allows you to move step by step based on what you are trying to find. For example, if you are performing a people search, you can easily navigate to relevant sections and access multiple tools in one place.
From practical experience, this tool saves a significant amount of time. Instead of searching randomly for tools online, you get a curated list that is regularly updated. This is especially helpful for beginners who may not know where to start, as well as for professionals who want a quick reference point.
Another advantage is flexibility. Since it links to multiple tools rather than locking you into one system, you can combine different resources to get better results. This makes it highly effective for both simple and complex investigations.
Overall, the OSINT Framework acts as a gateway into the world of OSINT, helping you discover, organize, and use the right tools more efficiently.
Best For:
- Beginners looking to explore OSINT tools in one place
- Researchers who need a structured approach to investigations
- Finding tools for people search, email lookup, and social media analysis
2. Google Dorks

Google Dorks is one of the most powerful yet underrated techniques in the OSINT space. Instead of relying on standard search queries, it uses advanced search operators to uncover hidden or hard-to-find information on the web. While many people use Google for basic searches, experienced users know that with the right commands, it can become a highly effective intelligence-gathering tool.
At its core, Google Dorking is about precision. You can use operators like site:, filetype:, intitle:, and inurl: to narrow down results and find exactly what you are looking for. For example, you can locate publicly exposed documents, login pages, or specific types of files that are not easily visible through normal searches. This makes it extremely useful for investigations, research, and even cybersecurity analysis.
From experience, one of the biggest advantages of Google Dorks is accessibility. You don’t need to install any software or sign up for a platform. All you need is a clear understanding of how search operators work. Once you get comfortable with it, you can uncover valuable insights within minutes.
However, it’s important to use this method responsibly. While the data you access is publicly available, it may still be sensitive. Ethical usage and awareness of legal boundaries are essential when applying these techniques.
Another key benefit is flexibility. Google Dorks can be combined with other OSINT tools to enhance results. For instance, you can use it to find usernames, email addresses, or documents, and then cross-check that data using other platforms for deeper analysis.
Overall, Google Dorks transforms a simple search engine into a powerful intelligence tool when used correctly.
Best For:
- Advanced web searches and uncovering hidden information
- Finding publicly exposed files and documents
- Supporting investigations with precise search queries
3. theHarvester

theHarvester is a well-known OSINT tool that focuses on gathering email addresses, subdomains, IPs, and other related data from public sources. If you are working on reconnaissance or early-stage investigation, this tool can quickly give you a strong starting point. It pulls information from multiple sources such as search engines, public databases, and key online services, which makes the data collection process much faster.
From experience, what makes theHarvester valuable is its efficiency. Instead of manually searching for emails or domain-related data, you can run a single command and get structured results within seconds. This is especially useful when you are trying to map out an organization’s online presence or identify potential points of contact.
Another strong aspect of this tool is its flexibility. It supports multiple data sources, allowing you to expand your search depending on your needs. Whether you are looking into a company, a domain, or a specific target, theHarvester adapts well to different use cases. It also integrates easily into larger workflows, which is helpful for professionals who rely on automation.
While it is a command-line tool and may seem technical at first, it becomes quite straightforward once you understand the basics. Many cybersecurity professionals and ethical hackers use it regularly because it delivers quick and reliable results without unnecessary complexity.
In practical terms, theHarvester helps you move from zero information to actionable insights in a very short time, making it a key tool for anyone involved in OSINT investigations.
Best For:
- Gathering emails, domains, and IP-related data
- Reconnaissance and initial investigation phases
- Cybersecurity professionals and ethical hackers
4. SecurityTrails API

SecurityTrails API is a powerful OSINT tool designed for collecting detailed domain and DNS-related data. If you have ever tried to track the history of a website or uncover its infrastructure, you know how complex that process can be. This is where SecurityTrails stands out. It provides deep insights into domain ownership, historical DNS records, IP mappings, and hosting data—all in a structured and easy-to-use format.
From experience, one of the most valuable aspects of SecurityTrails is its historical data. Instead of just showing the current state of a domain, it allows you to look back in time. You can see how a domain has changed, which IPs it was connected to, and how its infrastructure evolved. This is extremely useful during investigations, especially when trying to identify patterns or hidden connections.
Another major advantage is its API-first approach. Developers and businesses can integrate SecurityTrails directly into their systems, making it a strong choice for scalable solutions. In modern app development, this kind of integration helps automate data collection and improves security features without requiring manual effort.
The platform is also designed with usability in mind. Even though it offers advanced data, the interface is clean and organized, making it accessible to both beginners and professionals. Whether you are analyzing a suspicious domain or conducting research on a company’s digital footprint, the tool delivers reliable and actionable insights.
Overall, SecurityTrails API bridges the gap between raw DNS data and meaningful intelligence, helping users understand the bigger picture behind online infrastructures.
Best For:
- Domain and DNS intelligence
- Tracking historical domain data and changes
- Developers and businesses needing API-based integration
5. BGPView

BGPView is a specialized OSINT tool that focuses on internet routing data, specifically Border Gateway Protocol (BGP) information. While it may sound technical at first, its purpose is quite practical. It helps you understand how data travels across the internet by showing relationships between IP addresses, networks, and autonomous systems (ASNs).
From experience, BGPView becomes extremely useful when you are trying to trace the origin of an IP address or analyze network ownership. Instead of guessing where traffic is coming from, you can clearly see which organization controls a specific range of IPs and how different networks are connected. This level of visibility is valuable in investigations, especially when dealing with suspicious traffic or unknown sources.
One of the strongest advantages of BGPView is its transparency. It pulls real-time and historical routing data from trusted sources and presents it in a simple, readable format. You don’t need to be a network engineer to use it effectively. Even with basic knowledge, you can extract meaningful insights about network infrastructure.
Another benefit is its speed and accessibility. The tool is web-based and free to use, which means you can quickly look up IPs, prefixes, and ASNs without setting up complex systems. This makes it a convenient addition to any OSINT workflow.
BGPView is often used alongside other tools to build a more complete picture. For example, after identifying a domain or IP using other OSINT methods, you can use BGPView to understand its network-level details and connections.
Overall, BGPView provides a deeper layer of insight into how the internet operates, making it an essential tool for anyone dealing with network intelligence and analysis.
Best For:
- Analyzing IP addresses and network ownership
- Understanding BGP routing and ASN relationships
- Supporting network-level investigations
6. Recorded Future’s Vulnerability Database
Recorded Future’s Vulnerability Database is a highly valuable OSINT resource focused on tracking and analyzing known security vulnerabilities. Instead of searching across multiple platforms for threat data, this tool brings everything into one place and presents it in a structured, intelligence-driven format. It collects data from public sources, security feeds, and research communities, making it easier to understand emerging risks.
From experience, what makes this tool stand out is its context. Many vulnerability databases simply list technical details, but Recorded Future goes a step further. It connects vulnerabilities with real-world threats, exploitation trends, and risk levels. This allows you to not only identify a vulnerability but also understand how serious it is and whether it is actively being used by attackers.
Another key strength is its real-time updates. Cyber threats evolve quickly, and having access to up-to-date information is critical. This tool continuously monitors new vulnerabilities and provides timely insights, helping users stay ahead of potential risks. Whether you are a security analyst or a researcher, this kind of intelligence can significantly improve decision-making.
The platform is also designed for usability. Even though the data is complex, it is presented in a clear and organized way. You can easily search for specific vulnerabilities, explore related threats, and analyze trends without feeling overwhelmed.
In practical use, this tool is often combined with other OSINT resources to build a complete security picture. For example, after identifying a system or domain, you can check for known vulnerabilities and assess potential risks.
Overall, Recorded Future’s Vulnerability Database helps transform raw security data into actionable intelligence, making it an essential tool for anyone focused on cybersecurity and risk assessment.
Best For:
- Tracking and analyzing security vulnerabilities
- Understanding real-world threat context
- Cybersecurity professionals and risk analysts
7. Triage Malware Sandbox
Triage Malware Sandbox is a powerful OSINT tool designed to analyze suspicious files and URLs in a secure, controlled environment. Instead of opening unknown files on your own system—which can be risky—you can upload them to this sandbox and observe their behavior safely. This approach is widely used in cybersecurity to detect malware, track malicious activity, and understand how threats operate.
From experience, what makes Triage especially effective is its depth of analysis. Once a file is submitted, the platform runs it in an isolated virtual environment and records everything it does. You can see network connections, file changes, system interactions, and even screenshots of the execution process. This level of visibility helps you quickly determine whether a file is harmless or potentially dangerous.
Another strong advantage is automation. The tool generates detailed reports without requiring manual effort, which saves a lot of time. Even if you are not deeply technical, you can still understand the results through its clear interface and structured output. For professionals, it also provides advanced data that can be used for deeper investigations.
Speed is another factor that stands out. Results are typically available within minutes, allowing you to make quick decisions. This is particularly useful when dealing with suspicious email attachments, unknown downloads, or links shared across platforms.
Triage Malware Sandbox also integrates well into broader workflows. Many analysts use it alongside other OSINT tools to connect malware behavior with larger investigation findings, creating a more complete picture of potential threats.
Overall, it acts as a safety layer in your research process, helping you analyze risks without exposing your own system.
Best For:
- Analyzing suspicious files and URLs safely
- Malware detection and behavioral analysis
- Cybersecurity researchers and analysts
8. Mitaka
Mitaka is a lightweight yet highly practical OSINT tool that allows you to quickly gather intelligence from multiple sources with minimal effort. Unlike more complex platforms, Mitaka focuses on speed and simplicity. It enables you to highlight or input indicators such as IP addresses, domain names, URLs, or file hashes, and instantly retrieve relevant information from various online services.
From experience, Mitaka is especially useful when you need quick answers without going through multiple tools manually. Instead of opening different websites one by one, it aggregates results in a single view. This makes your workflow much more efficient, particularly during time-sensitive investigations.
One of its key strengths is browser integration. Mitaka is available as a browser extension, which means you can use it directly while browsing the web. If you come across a suspicious link or unknown data point, you can analyze it instantly without leaving the page. This seamless experience makes it a favorite among analysts who prefer working in real time.
Another advantage is its accessibility. You don’t need deep technical knowledge to use Mitaka effectively. The interface is simple, and the results are easy to understand. At the same time, it still provides enough depth for professionals who want to dig deeper into the data.
Mitaka also supports multiple data sources, which improves the reliability of the information you receive. By combining results from different platforms, it helps you build a clearer and more accurate picture.
Overall, Mitaka is a fast and efficient tool that simplifies everyday OSINT tasks, making it a valuable addition to any toolkit.
Best For:
- Quick lookups of IPs, domains, and hashes
- Real-time analysis through browser integration
- Users who need fast and simple OSINT insights
9. Recorded Future’s Browser Extension
Recorded Future’s Browser Extension is designed to bring real-time threat intelligence directly into your browsing experience. Instead of switching between multiple platforms, this tool allows you to access valuable insights instantly while you navigate websites, analyze links, or review online data. It works quietly in the background and enhances your awareness without interrupting your workflow.
From experience, the biggest advantage of this extension is context. When you visit a website or come across an IP address or domain, the tool automatically provides risk scores, threat indicators, and relevant intelligence. This means you don’t have to manually investigate every element—you get immediate insights that help you decide whether something is safe or suspicious.
Another strong feature is its integration with Recorded Future’s intelligence network. The extension pulls data from a wide range of sources, including threat feeds, research reports, and historical data. This ensures that the information you receive is not only fast but also reliable and well-supported.
Ease of use is also a major benefit. The extension is simple to install and does not require advanced technical skills. Once active, it becomes a natural part of your browsing process. Whether you are researching a domain, reviewing links, or analyzing online activity, the tool provides useful insights right when you need them.
It also helps improve efficiency. Instead of performing separate searches, you can make faster decisions based on the data presented in real time. This is particularly useful for professionals who deal with large volumes of information daily.
Overall, Recorded Future’s Browser Extension enhances your ability to analyze online data quickly and confidently, making it a valuable tool for both beginners and experienced users.
Best For:
- Real-time threat intelligence during web browsing
- Quick risk assessment of domains and links
- Users who want seamless OSINT integration into daily workflows
10. Have I Been Pwned?
Have I Been Pwned? is one of the most widely used OSINT tools for checking whether an email address or phone number has been exposed in a data breach. In today’s digital world, where data leaks are increasingly common, this tool provides a simple yet powerful way to understand your exposure and take action before it becomes a bigger problem.
From experience, this is often one of the first tools people should use when assessing their online security. You simply enter an email address, and within seconds, the platform shows whether it has appeared in any known breaches. It also provides details about the affected services and the type of data that may have been compromised, such as passwords, usernames, or personal information.
What makes this tool especially valuable is its reliability. It is regularly updated with data from verified breaches, ensuring that the results are accurate and relevant. This helps users stay informed about potential risks without needing advanced technical knowledge.
Another key benefit is awareness. Many people are unaware that their data has been exposed until it is too late. This tool helps bridge that gap by making breach information accessible and easy to understand. It also encourages better security practices, such as updating passwords and enabling two-factor authentication.
In practical use, Have I Been Pwned? is often combined with other OSINT tools to build a broader understanding of digital identity and exposure. It plays an important role in both personal security and professional investigations.
Overall, it is a simple but essential tool that helps you stay one step ahead in protecting your digital presence.
Best For:
- Checking email and phone number exposure in data breaches
- Improving personal and organizational security awareness
- Quick and reliable breach verification
11. BuiltWith
BuiltWith is a highly effective OSINT tool that helps you understand the technology stack behind any website. Instead of guessing what tools or platforms a site is using, BuiltWith gives you a clear breakdown of everything from hosting providers and analytics tools to content management systems and frameworks.
From experience, this tool is extremely useful when you want to analyze how a website is built or identify the technologies powering it. You simply enter a domain, and within seconds, you get a detailed report showing the tools and services being used. This can include things like tracking scripts, eCommerce platforms, advertising networks, and more.
One of the biggest advantages of BuiltWith is its clarity. The data is presented in a structured way, making it easy to understand even if you are not highly technical. At the same time, it provides enough depth for developers, marketers, and researchers who want detailed insights.
It is also very useful for competitive analysis. Businesses often use BuiltWith to study competitors, identify trends, and understand which technologies are popular in a specific industry. This can help in making better strategic decisions, especially when planning new projects or improving existing platforms.
Another practical use is in security and investigation workflows. By understanding the technologies a website uses, you can identify potential vulnerabilities or points of interest for further research.
Overall, BuiltWith turns technical website data into actionable insights, making it a valuable tool for both research and decision-making.
Best For:
- Identifying technologies used by websites
- Competitive analysis and market research
- Supporting development and security investigations
12. Shodan
Shodan is often described as a search engine for the internet’s connected devices, and from experience, that description is very accurate. Unlike traditional search engines that index websites, Shodan scans and indexes devices such as servers, cameras, routers, and IoT systems. This makes it an incredibly powerful tool for understanding what is exposed online and how systems are connected.
What sets Shodan apart is its ability to reveal information that is not typically visible through normal browsing. By entering an IP address, domain, or even a specific query, you can discover open ports, running services, software versions, and sometimes even security weaknesses. This level of visibility is extremely useful for cybersecurity professionals who need to assess risks and monitor exposure.
Another key advantage is its real-time data collection. Shodan continuously scans the internet and updates its database, ensuring that the information remains current. This allows users to identify changes quickly and respond to potential threats without delay.
Despite its advanced capabilities, Shodan is surprisingly easy to use. The interface is clean, and basic searches can be performed without deep technical knowledge. At the same time, it supports advanced filters and queries for users who want more precise results.
In practical scenarios, Shodan is often used to identify misconfigured systems, monitor network security, and support investigations. It is also valuable for organizations that want to understand their own digital footprint and reduce unnecessary exposure.
Overall, Shodan provides a unique perspective on the internet, helping users see beyond websites and into the infrastructure that powers them.
Best For:
- Discovering internet-connected devices and services
- Identifying exposed systems and potential vulnerabilities
- Cybersecurity monitoring and network analysis
13. SpiderFoot
SpiderFoot is a highly versatile OSINT automation tool that helps you collect and analyze data from a wide range of sources with minimal manual effort. Instead of running multiple tools separately, SpiderFoot brings everything together into one unified platform. It automates the process of gathering intelligence related to domains, IP addresses, email addresses, usernames, and more.
From experience, what makes SpiderFoot stand out is its automation capability. Once you start a scan, the tool runs dozens of modules in the background, each designed to collect specific types of information. It then compiles the results into a structured report, allowing you to quickly understand relationships, risks, and patterns.
Another major strength is its flexibility. You can customize scans based on your needs, choosing which modules to run and how deep the analysis should go. This makes it suitable for both quick checks and detailed investigations. Whether you are looking for exposed data, security risks, or digital footprints, SpiderFoot adapts to different use cases.
The interface is also user-friendly, especially considering the depth of data it provides. Results are organized clearly, often with visual elements that help you see connections between different data points. This makes it easier to interpret complex information without getting overwhelmed.
SpiderFoot is widely used in cybersecurity, investigations, and research. It is particularly valuable for professionals who need continuous monitoring and automated intelligence gathering.
Overall, SpiderFoot simplifies complex OSINT workflows by combining automation, flexibility, and detailed reporting into a single tool.
Best For:
- Automated OSINT data collection and analysis
- Identifying digital footprints and security risks
- Users who need scalable and customizable investigations
14. Maltego
Maltego is one of the most advanced OSINT tools available, known for its powerful data visualization and link analysis capabilities. Instead of just presenting raw data, it helps you see relationships between people, domains, email addresses, organizations, and more through interactive graphs. From experience, this visual approach makes complex investigations much easier to understand and manage.
What makes Maltego stand out is its ability to connect data from multiple sources and display it in a meaningful way. You can start with a single piece of information—such as a name, email, or domain—and expand it using built-in transforms. These transforms pull additional data from various sources and map out connections automatically. This process helps uncover hidden relationships that might be missed with traditional tools.
Another key strength is its scalability. Maltego is used by both individual researchers and large organizations. It supports small investigations as well as complex, large-scale data analysis. The platform also integrates with external data providers, allowing you to extend its capabilities even further.
Although it may seem complex at first, the interface becomes intuitive once you get familiar with it. The drag-and-drop functionality and visual graphs make it easier to explore data without getting lost in text-heavy reports.
Maltego is particularly useful in investigations where relationships matter. Whether you are analyzing networks, tracking digital identities, or conducting research, the ability to visualize connections provides a major advantage.
Overall, Maltego transforms raw data into visual intelligence, helping you see the bigger picture more clearly and make better-informed decisions.
Best For:
- Visualizing relationships between data points
- Complex investigations and link analysis
- Professionals handling large-scale OSINT research
15. Nmap
Nmap, short for Network Mapper, is one of the most trusted and widely used tools for network discovery and security auditing. It has been around for years, and from experience, it remains a core tool for anyone working in cybersecurity or technical investigations. While it is more technical compared to other OSINT tools, its capabilities are extremely powerful when used correctly.
At its core, Nmap helps you scan networks and identify active devices, open ports, and running services. This information is critical when you want to understand how a system is structured or detect potential security gaps. Instead of guessing what is happening behind a network, Nmap gives you a clear and detailed view.
One of the biggest strengths of Nmap is its flexibility. You can run simple scans for quick insights or perform advanced scans with detailed configurations. It supports a wide range of options, allowing you to customize your approach based on your needs. This makes it suitable for both beginners who are learning and professionals who require in-depth analysis.
Another advantage is its accuracy and reliability. Nmap is known for delivering precise results, which is why it is widely trusted across the cybersecurity community. It also supports scripting, which allows users to automate tasks and extend its functionality even further.
In practical use, Nmap is often combined with other OSINT tools to build a complete understanding of a target. For example, after identifying a domain or IP, you can use Nmap to analyze its network structure and detect potential vulnerabilities.
Overall, Nmap is a foundational tool that provides deep insights into network environments, making it essential for technical users and security professionals.
Best For:
- Network scanning and security auditing
- Identifying open ports and active services
- Advanced users and cybersecurity professionals
How OSINT Tools Impact App Development and Digital Platforms
OSINT tools are no longer limited to investigations or cybersecurity. They are now playing a major role in shaping how modern digital platforms are built and managed. From experience, many developers and businesses are quietly integrating OSINT capabilities into their systems to improve trust, safety, and overall user experience.
Enhancing Modern App Development
In today’s competitive market, users expect more than just functionality—they expect security and reliability. This is where OSINT tools add real value in app development. Developers can integrate data intelligence features that help verify users, detect suspicious activity, and reduce fake accounts. Instead of building these systems from scratch, OSINT tools provide ready-to-use solutions that save both time and effort.
Reducing Dating App Cost and Operational Risks
One of the biggest challenges for online platforms, especially dating services, is maintaining authenticity. Fake profiles, scams, and misuse can quickly damage user trust. By using OSINT tools, platforms can automate identity checks and flag suspicious behavior early. This reduces the need for manual moderation, which directly impacts the overall dating app cost by lowering operational expenses.
Improving Safety in Hookups Apps
Safety is a major concern in hookups apps, where users often interact with strangers. OSINT tools help address this issue by enabling background checks, image verification, and behavior analysis. This creates a safer environment for users and increases platform credibility. From experience, apps that invest in these features tend to retain users for longer because trust plays a key role in engagement.
Supporting Creator Platforms and Fan-Based Ecosystems
With the rise of subscription platforms and Fanvue Alternatives, identity verification has become even more important. Users want to ensure that creators are authentic, while platforms need to prevent impersonation and fraud. OSINT tools support these needs by offering quick verification methods and monitoring digital footprints.
Building Trust Through Data Intelligence
Ultimately, OSINT tools help platforms move from reactive to proactive systems. Instead of responding to issues after they happen, businesses can prevent them by using real-time data insights. This not only improves security but also enhances user confidence.
In simple terms, OSINT is becoming a core part of modern digital infrastructure. It helps developers build smarter, safer, and more efficient platforms that meet the expectations of today’s users.
Best Practices for Using OSINT Tools Safely and Ethically
OSINT tools are powerful, but with that power comes responsibility. From experience, the difference between effective use and misuse often comes down to awareness and intent. If you follow a few simple practices, you can use these tools confidently while staying within ethical and legal boundaries.
1) Understand Legal Boundaries
Even though OSINT relies on publicly available data, that does not mean everything is free to use without limits. Different countries have different data protection laws, and it’s important to respect them. Always make sure your research stays within legal guidelines and avoids accessing restricted or sensitive information in an improper way.
2) Use Data Responsibly
One of the most important rules is to avoid making assumptions based on incomplete data. OSINT tools provide insights, but they do not always tell the full story. From experience, it’s always better to cross-check information using multiple sources before drawing conclusions. This helps prevent errors and ensures accuracy.
3) Respect Privacy
Just because information is available online does not mean it should be misused. Respecting privacy is essential when using OSINT tools. Avoid sharing personal data unnecessarily or using it in a way that could harm someone. Ethical use builds trust and keeps your work credible.
4) Avoid Over-Reliance on a Single Tool
No single tool provides complete information. Each platform has its own strengths and limitations. That’s why it’s important to combine multiple tools and approaches. This not only improves accuracy but also gives you a more balanced view of the data.
5) Stay Updated with Tools and Techniques
OSINT is constantly evolving. New tools, features, and techniques are introduced regularly. Staying updated helps you use tools more effectively and ensures that your methods remain relevant. It also helps you adapt to changes in data availability and technology.
6) Protect Your Own Digital Footprint
While conducting research, don’t forget about your own privacy. Use secure connections, avoid exposing your personal information, and be mindful of the platforms you interact with. Maintaining your own security is just as important as analyzing others.
In the end, using OSINT tools safely is about balance. When you combine technical skills with ethical awareness, you not only get better results but also ensure that your work remains responsible and trustworthy.
Wrap up
OSINT tools have transformed the way we search, verify, and analyze information in the digital world.
Throughout this guide, you’ve seen how the best OSINT Tools help simplify people and face search, how different tools serve specific purposes from data collection to network analysis, and how they are now deeply integrated into modern platforms and workflows. More importantly, you’ve learned that using these tools effectively is not just about access to data, but about understanding how to use that data responsibly and strategically.
As online interactions continue to grow, the ability to verify identities and detect risks will only become more important. Whether you are an individual trying to stay safe, a developer building secure platforms, or a professional conducting investigations, OSINT tools give you a clear advantage.
If you want to take this further, explore how to build your own OSINT workflow or toolkit tailored to your needs. That’s where you move from just using tools to mastering them.
FAQs
Are OSINT tools legal to use?
Yes, OSINT tools are legal as they rely on publicly available information. However, how you use that data matters. You should always follow local laws and avoid using the information for harmful or unethical purposes. Responsible usage is key to staying compliant.
Do OSINT tools work on private social media accounts?
No, OSINT tools cannot directly access private accounts or restricted data. They only collect information that is publicly available. However, they can sometimes provide indirect insights by analyzing related public data, connections, or shared content.
Can beginners use OSINT tools without technical knowledge?
Yes, many OSINT tools are designed for beginners and have simple interfaces. Tools like frameworks and browser-based platforms are easy to use. However, more advanced tools may require basic technical understanding as you progress.
How accurate are OSINT tools for face search?
Accuracy depends on factors like image quality, database size, and the tool being used. While modern tools are quite advanced, results are not always 100% reliable. It’s always a good idea to verify findings using multiple sources before making decisions.
Can OSINT tools be automated for large-scale use?
Yes, many advanced OSINT tools offer automation features such as APIs and integrations. These allow businesses and professionals to run large-scale searches, monitor data continuously, and receive real-time updates without manual effort.